Insights
Threat context through a SAFE lens.
Short executive perspectives on how modern threat patterns should shape architecture decisions before initiatives launch.
Featured insight
Q1 2026 Cyber Incident Landscape
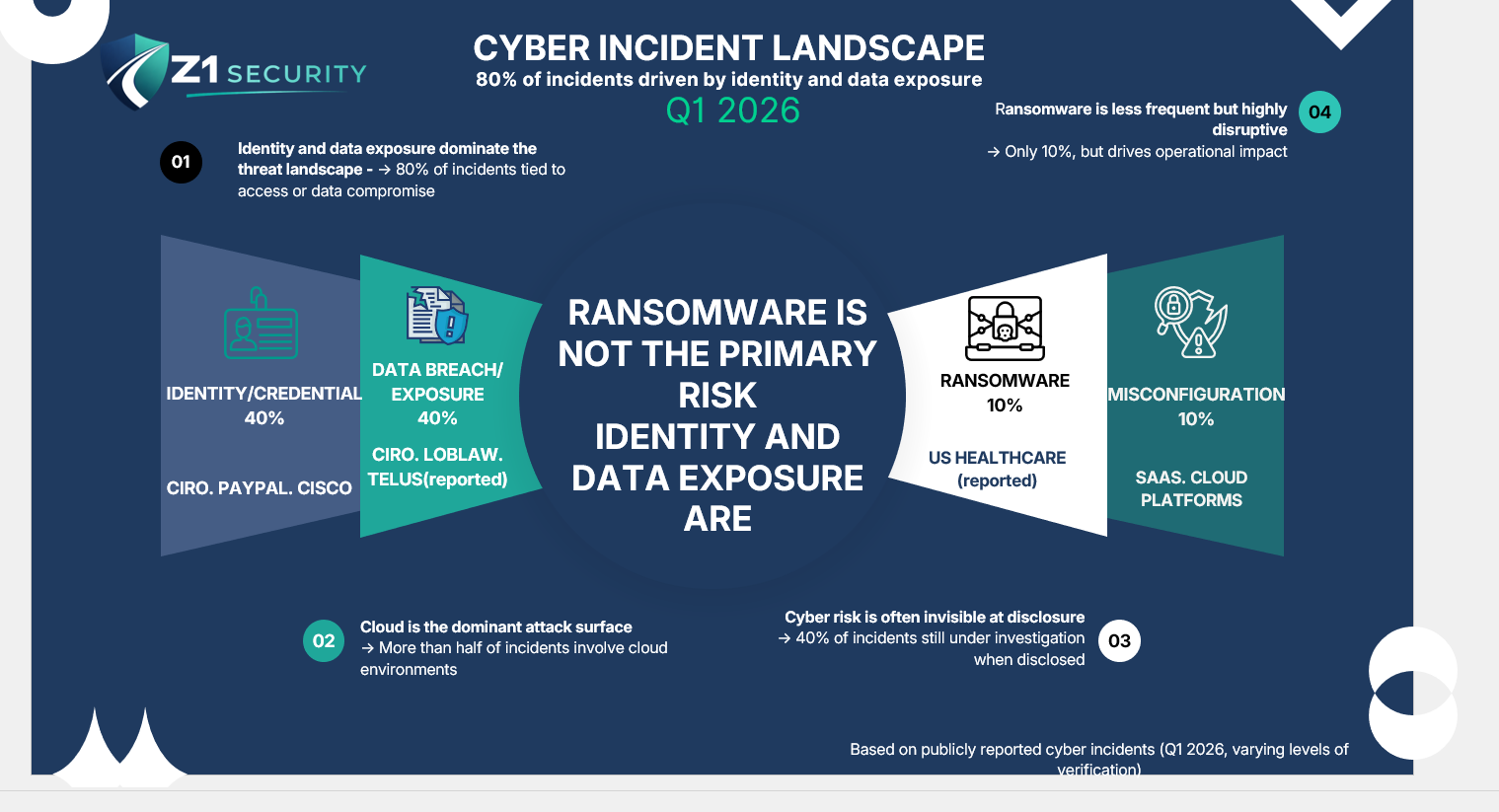
Executive takeaway
What leaders should take from this
Identity and data compromise often precede disruption.
Architecture decisions shape exposure before controls catch up.
Third-party and cloud pathways expand attack surface.
Why proactive architecture matters now
Threats increasingly exploit design decisions.
CISA describes ransomware and data extortion as increasingly destructive and impactful, including data theft and pressure to release stolen data. Microsoft reports that financially motivated attacks include data theft, extortion, ransomware, and destructive activity.
The SAFE takeaway: do not wait for a generic assessment after design decisions are locked. Review identity, data, integrations, and controls before the rollout path is hard to change.
Future topics
Architecture decisions worth examining
Copilot and AI onboarding risk
Identity lifecycle integrity
Privileged access failure modes
Vendor integration exposure
Analytics data leakage
Data-centric security patterns
