Intake & Architecture Review
- Scope and objectives
- Stakeholders
- Data flows
- Integrations
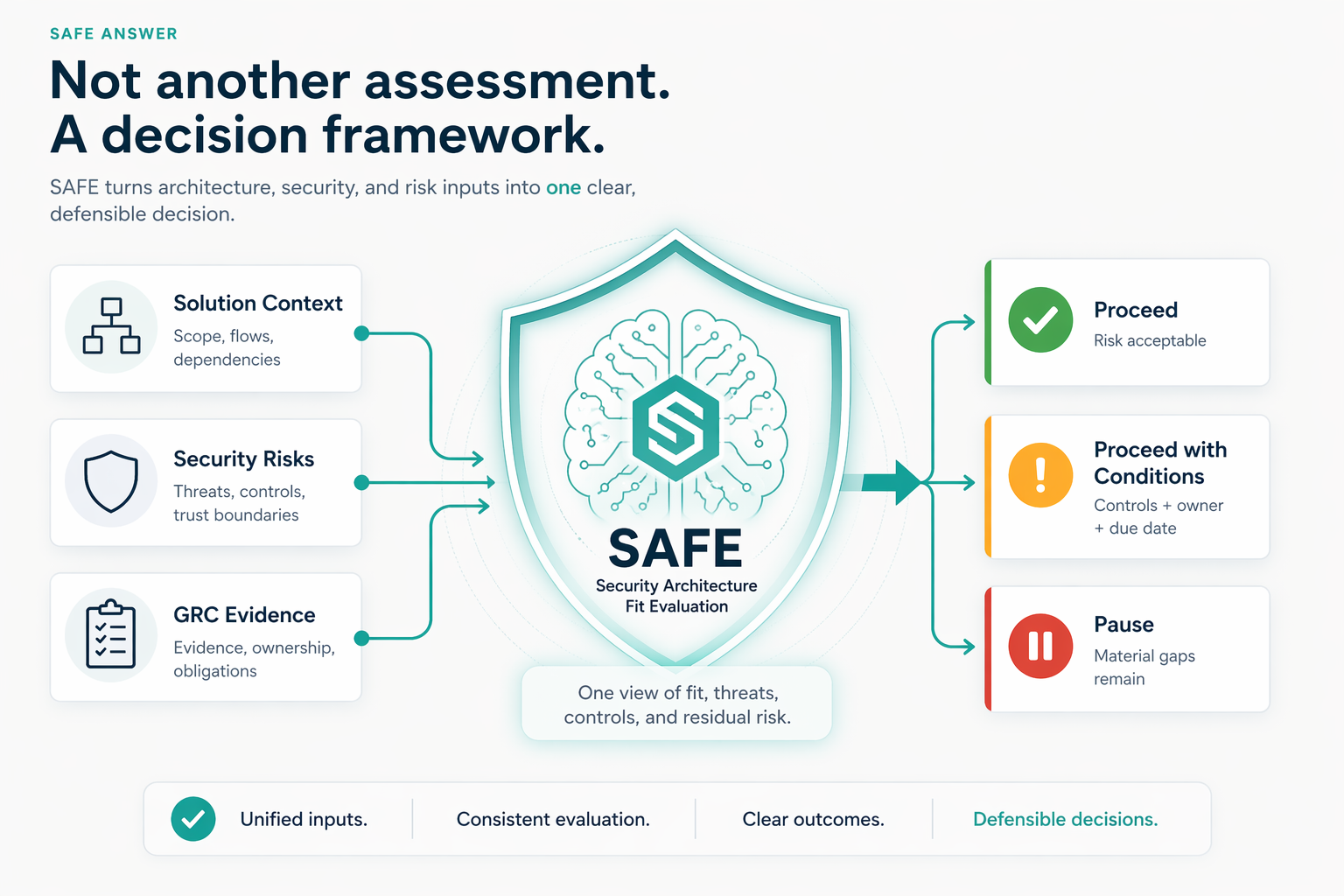
SAFE helps leaders decide: proceed, proceed with conditions, or pause before new SaaS, AI, cloud, or vendor risk becomes costly to reverse.
One decision path across architecture, security, GRC, evidence, and business risk.
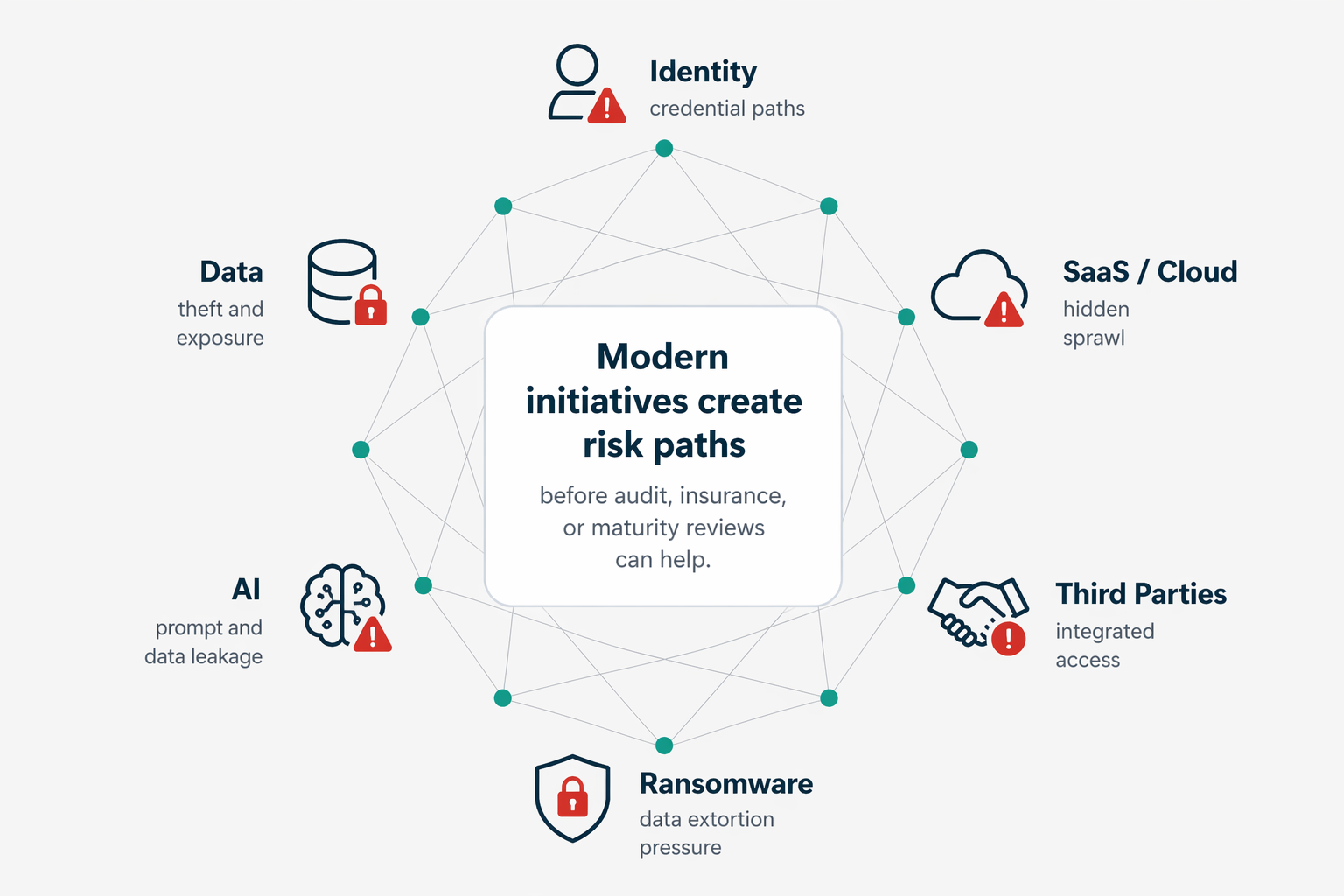
Ransomware and extortion actors increasingly use data theft, identity compromise, SaaS/cloud exposure, and third-party access as leverage. Architecture decisions made today become tomorrow's breach paths if they are not reviewed early.
Solution architects move fast, security teams focus on critical projects, and GRC teams face review backlogs. SAFE was built to close the gaps before delivery risk grows.
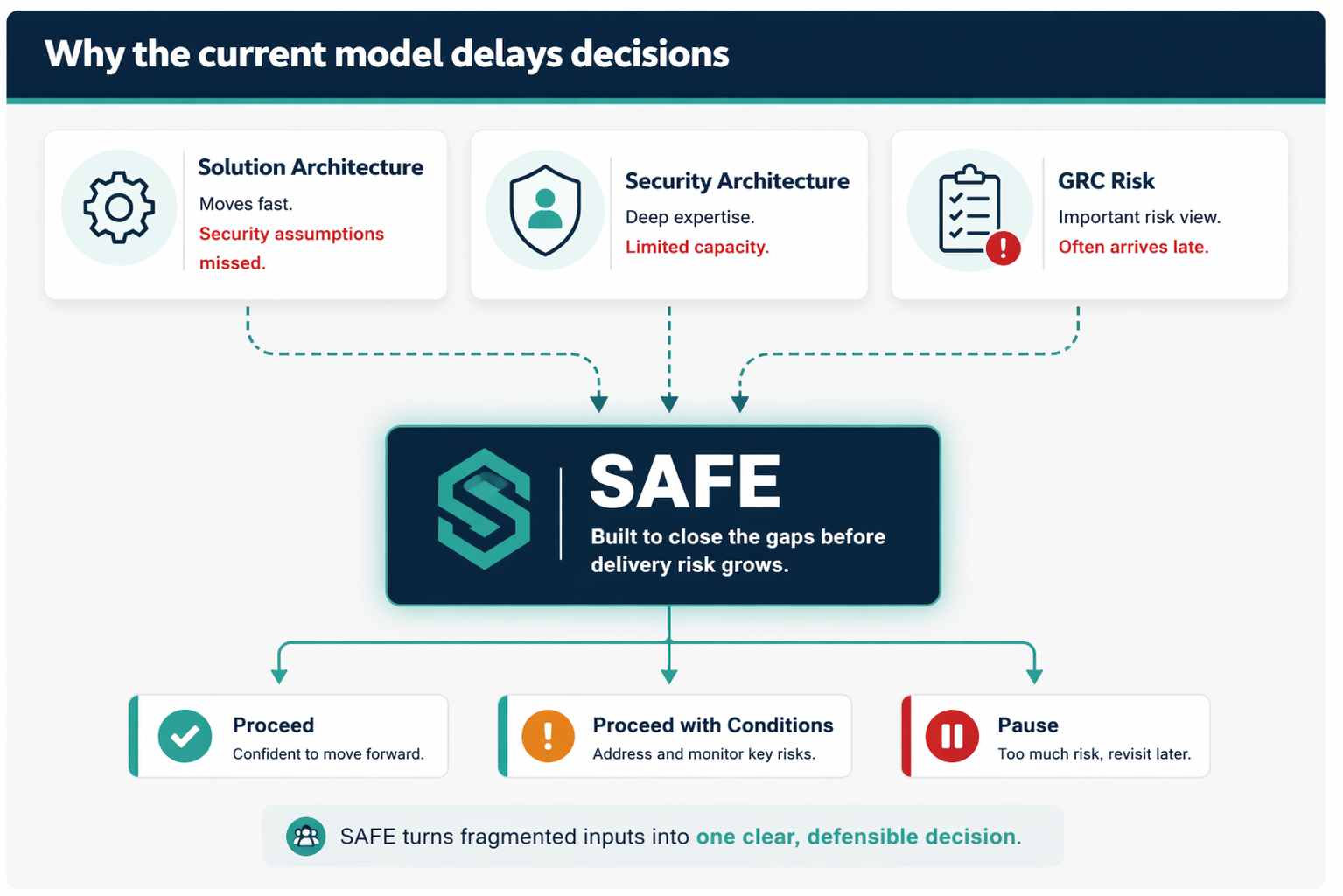
SAFE converts architecture, security, and risk complexity into a defensible decision path.
Audit, insurance, and maturity reviews all matter. SAFE focuses on the decision in front of the business: Are we safe enough to proceed?
When stakeholders are responsive and core materials are available.
Engagements are scoped based on architecture complexity, integrations, data sensitivity, stakeholder availability, and evidence depth. Z1 provides fixed-fee options after scoping.
Best when the initiative is bounded and leaders need a fast proceed, conditional, or pause decision.
Explore SAFEBest for PII, PCI, PHI, HR, financial, client-confidential, AI, cloud, or multi-system environments.
Explore SAFE+Useful for internal audit, GRC, cyber insurers, external assessors, and executive assurance.
Explore ValidateUseful when new tools, integrations, vendors, cloud changes, and AI use cases keep arriving.
Discuss RetainerUseful for repeatable SaaS, identity, data, AI, cloud, and vendor patterns.
Discuss PatternsSaaS onboarding, AI tools, cloud changes, vendor integrations, data platforms, identity changes, and executive decision gates.